A new Stuxnet-level vulnerability named Simjacker used to secretly spy over mobile phones in multiple countries for over 2 years: Adaptive Mobile Security reports - Security Boulevard

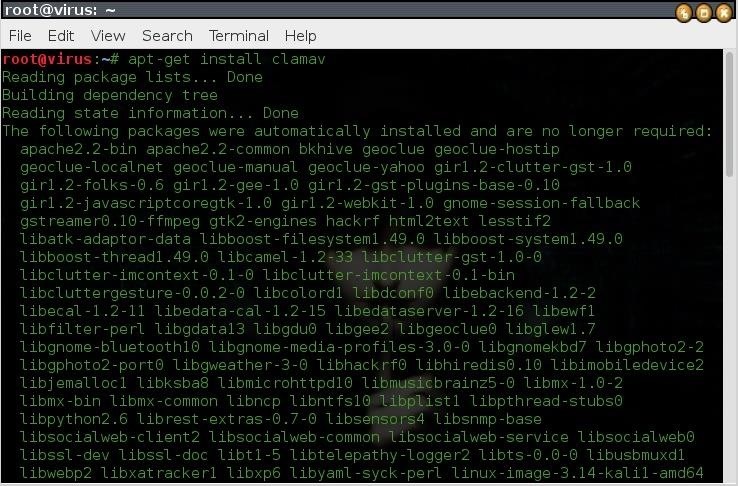
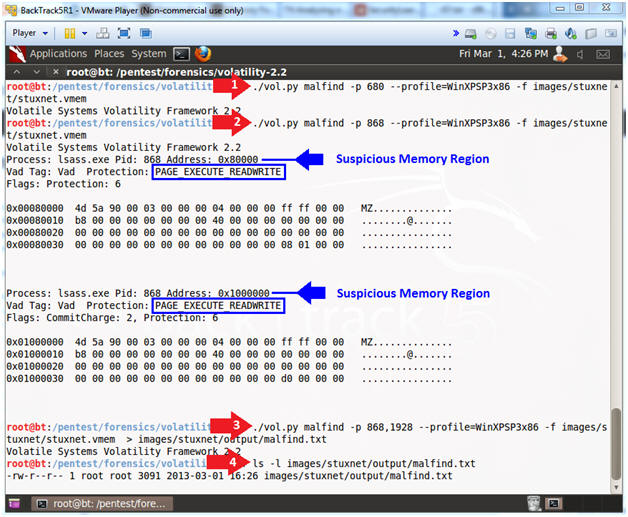
Memory Forensics: Analyzing a Stuxnet Memory Dump (And you can too!) – CYBER ARMS – Computer Security